Case Study #1 Why Windows Patches lead to Computer Crashes
On the second Tuesday of each month, Microsoft issues patches on what has become known as Patch Tuesday. Unfortunately, Patch Tuesday leads to Crash Wednesday. Windows 10 downloads and installs patches whenever it pleases, and then reboots the computer.
On August 13, 2019, Microsoft released patches for 93 security flaws. The most dangerous of these flaws were four remote code execution (RCE) flaws that take advantage of holes in Windows Remote Desktop Service (RDS). The numbers for these flaws are CVE-2019-1181, CVE-2019-1182, CVE-2019-1222, and CVE-2019-1226.
But the notice included a total of 29 remote execution flaws affecting nearly every type of Windows program from MS Word to MS Outlook. 11 of the 29 critical flaws are present in or are a key component of the browsers built into Windows. Hackers can exploit any of these 29 Remote Code Execution flaws to take over a computer and then spread malware to other computers on the same network without any user interaction. But the Excel spreadsheet for all of the flaws actually listed 2,977 flaws being patched – making this one of the biggest patches in MS history.
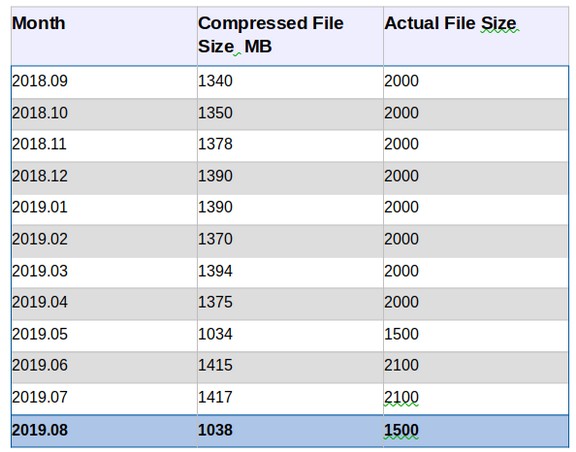
The file size for just the August 2019 Update was 1038 Megabytes (over 1 Gigabyte). This is why every month that Windows is on your computer, it takes over more and more space on your hard drive. My high speed connection took over 5 minutes just to download this monster. Extracting the folder and opening it showed another zipped 1.1 GB folder. Extracting this monster showed 5 more zipped folders. The largest was 387 MB. Extracting just this one folder showed it contained over 7000 files.
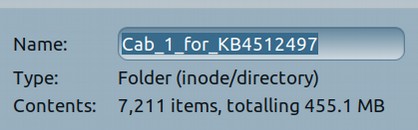
The second folder contained another 7000 files. My guess is that all five folders contain over 20,000 files. The total uncompressed file size was 1.5 gigabytes.
Update File Size by Month… Each month Windows patches increase the file size by 1 to 2 GB:
For those keeping score, this is the fifth time in 2019 Microsoft has had to fix critical security issues with its Remote Desktop service. Updates to Windows 10 alone caused serious problems for users in January, April, October and November 2018 as well as February 2019 prior to the current ‘Awful April’.
Case Study #2: Cozy Bear Strikes Again
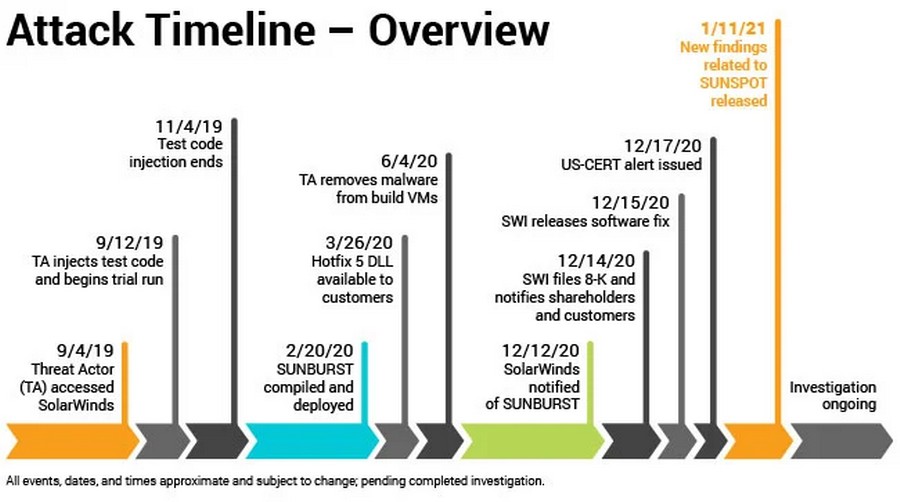
After another year of record-breaking ransomware attacks on businesses using Windows computers, on December 13, 2020, a security firm called Fire Eye, announced that some unknown hacker(s) had compromised a widely used software program called Solar Winds: “The trojanized update file masquerades as a standard Windows Installer Patch. After an initial dormant period of up to two weeks, the malware retrieves and executes commands, called “Jobs”, that include the ability to transfer files, execute files, profile the system, reboot the machine, and disable system services.”
It was a supply chain attack meaning that it was an attack on Solar Winds that they then spread around the world, including to many US government agencies. Solar Winds is a Windows program intended to remotely monitor Windows servers. The pricing of Solar Winds Server & Application Monitor, that scales to support hundreds of servers and thousands of applications, starts at $3000.
Solar Winds is used by hundreds of thousands of organizations around the world, including 425 Fortune 500 companies and multiple US federal agencies. Solar Winds estimated 18,000 customers were infected – but the real number is likely to be much higher. Solar Winds said its technology is used by the Pentagon, all five branches of the US military, the State Department, NASA, the NSA, the Postal Service, the National Oceanic Atmospheric Administration, the Department of Justice, and the Office of the President of the United States. Financial losses will be in the hundreds of billions of dollars. Solar Winds is also used by Dominion meaning that the hackers almost certainly had the ability to alter election results in November 2020.
Another security firm has been tracking this hacker for years.
“Volexity has been able to tie these attacks to multiple incidents it worked in late 2019 and 2020. Volexity found multiple tools, back doors, and malware implants that had allowed the attacker to remain undetected for several years. After being extricated from the network, Dark Halo then returned a second time, exploiting a vulnerability in the organization’s Microsoft Exchange Control Panel.
The Washington Post, owned by Jeff Bezos and bought with money given to him by the CIA, immediately blamed Russia and Cozy Bear. The irony of this accusation is that I proved years ago that Cozy Bear was actually the NSA working with the CIA using the Marble program.
Connecting hundreds of thousands of Windows based Local System Accounts to remote administrators is simply begging for a cyber attack. Since Windows servers are loaded with back doors, there is really no need to hack Solar Winds.
Comments on Reddit confirmed that the malware was still on Solar Winds servers even after the hack had been exposed:
"Hmm not to be a wet blanket or anything but I literally just downloaded the infected installer from the Solar winds website and extracted the installer and found that the back door DLL is definitely still contained in the installer on the website literally right now"
Note: DLL stands for a Windows Dynamically Linked Library which is commonly used by hackers to hack Windows servers.
https://www.reddit.com/r/Solarwinds/comments/kcpqn4/russian_hackers_use_solarwinds_to_breach_us/
Case Study #3 12 Million People harmed by Parler Epik Fiasco
In January 2021, Amazon, Twitter, Google, Facebook and Microsoft (aka the tech monopoly billionaires) combined to shut down Parler -a social network used by more than 12 million people. This was done at the same time that more than 100,000 people – including President Donald Trump – had their Facebook and Twitter accounts canceled – leaving them with a greatly reduced ability to reach out to their supporters and communicate with each other. Gmail, Shopify and PayPal also removed accounts “associated” with Trump.
This coordinated attack by tech billionaires was the worst crime of censorship in the history of humanity. I say crime because this form of extreme censorship is a clear violation of the 1st Amendment to the US Constitution – in addition to violating the private property rights of Parler who lost an extremely valuable business despite being LESS involved in promoting the US Capitol riots than Facebook and Twitter!
I have been warning people for years about the dangers of placing all of our social media eggs in baskets controlled by billionaires. My hope is that, after this latest nightmare, business people will start waking up and realizing that there is a war going on against us – and we are losing badly.
Parler Problems
The most obvious mistake Parlor executives made was hosting their platform on servers controlled by Amazon billionaire Jeff Bezos. Jeff was given over $600 million by the US Deep State (aka CIA). So when the Deep State says JUMP, Jeff says How High?
Parler (and Trump) also used Google for their email services. I have a free Gmail account. But I also have a free Proton Mail account that I use for more important matters.
Parler has since moved to a web hosting company called Epik which is located in Sammamish Washington (just east of Seattle). Epik has its own set of problems. Unlike Amazon, Microsoft, Google and Facebook, Epik actually does not have their own server farm. It is possible that Epik does not even have a single thousand dollar server. Instead, Epik rents space on servers owned by others.
For example, Epik used to rent space on Voxility servers. This ended on August 5, 2019, when Voxility terminated their server contract with Epik. Epik then moved on to Linode servers. This ended on August 9, 2020 when Linode terminated their server contract with Epik. It is not clear where Epik is now renting server space. But where ever it is, it is likely just a matter of time before that to is taken down.
Perhaps this is why Epik has denied any relationship with Parlor. Robert Davis, Epik VP said they are not in talks with Parler about hosting the site and have no plans to do so: “We’ve had no connection, no correlation, nothing to do with Parler.” In the past, Epik has been linked to controversial right-wing sites, such as InfoWars and Gab. However, Epik said it no longer hosts those sites.
The underlying problem is that, thanks to the US Patriot Act, any server company in the US can be forced by the Deep State to take down any website the Deep State does not like in less than 24 hours – and without any court hearing. I started writing about this problem almost 10 years ago after several businesses were wiped out by the Deep State without any legal hearing. This is why all of my websites are located on servers in Canada rather than on servers in the US. At least in Canada, you still get to have your case heard by a judge before your business is wiped out.
The real problem is top down control of social platform communications. The only long term solution to this problem is bottom up local control of your data and your social connections. This requires learning about bottom up web technology to protect your business. It is the only way that business owners will stand a chance against the billionaire tech monsters that are currently in control of social media here in the US. We can win this technology and information war – and defeat censorship and save democracy. But it is going to require business owners to have a much higher technology skill set than most currently have.
This is why years ago, I started College in the Clouds dot org. It was because I knew this day was coming. Now that it is obviously here, I hope you take some time to visit that website and learn how you can protect your business by becoming more familiar with Linux and other free open source web building tools.