V. History of Xbot
If you do a Google search for the term Xbot, you will see these two definitions in the Urban Dictionary:
1. A creature that dwells in the depths of Microsoft, (so loyal to Microsoft that they) create flame wars with anyone that dares to insult Microsoft in anyway.
2. A person who is blindly, fanatically loyal to Microsoft.
While forks refusing to see the security flaws of the Windows operating system even when they are the victims of these flaws is a problem, in this article, I use the term Xbot not to refer to Microsoft Fan Boys but rather to refer to the evolution of a hacking tool created beginning in 2007 and continuing to the present day. The term botnet or bot in malware refers to
“a type of malware that secretly takes hold of a large network of machines and can be exploited to perform malicious tasks without the victim being aware.” As the UEFI hacking tool relies on the user lack of awareness, Xbot is the perfect name for it.
The first public reference to this NSA tool was in a Snowden document, published by Der Spiegel in 2015. The Der Spiegel articl included a copy of a Job Announcement issued on July 11, 2006 by the NSA “Persistence Division” looking for programmers to develop EFI firmware hacking tools beginning in January 2007. Here is a quote from this NSA job announcement:
“BERSERKR is a persistent backdoor that is implanted into the BIOS and runs from SMM… There is a prototype that Works on Windows 7 but this also needs to work on Windows 2008.”
Here is an image of the 2006 NSA job announcement:
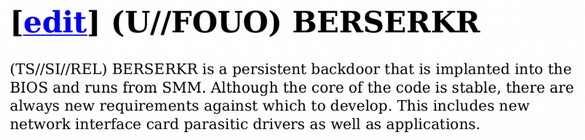
The firmware implant (Berserkr) hides from the user on a hidden Partition that cannot be seen or accessed by the user but which can be activated by a secret “hook” or custom command. http://www.spiegel.de/media/media-35661.pdf
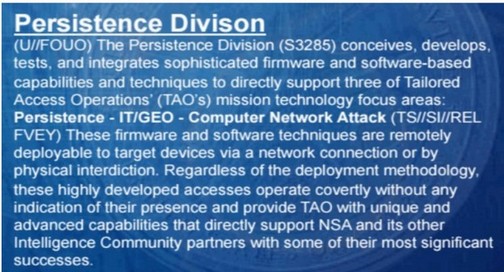
The following image is from a 2007 NSA Slideshow supplied by Snowden and made public by the Intercept on January 24 2019. The NSA and its Sub-contractors have at least 100,000 hackers.
https://theintercept.com/document/2019/01/24/tailored-access-operations-2007/
This is slide 7 which describes the mission of the NSA Persistence Division which is part of the NSA Access Tech Division. Note the emphasis on remote access to Firmware and working with their “community partners” aka Microsoft and Intel. Another January 2007 NSA document referred to Supply Chain attacks using “Sierra Mist” which is a hidden partition on nearly all hard drives used to compromise “Firmware BIOS”.
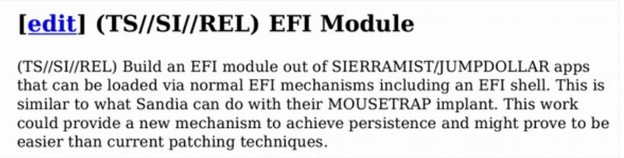
Note that the Sierra Mist Cyber Weapon is intended to be placed as a module inside of a EFI module. EFI refers to the Extensible Firmware Interface (which is now known as UEFI or the Unified Extensible Firmware Interface). What is extremely strange about creating a persistent cyber weapon to be placed inside of an EFI module is that not a single commercial computer in the world used EFI or UEFI in 2007.
In fact, UEFI was not introduced on Windows servers until 2009 and was not introduced on Windows computers until the introduction of Windows 8 in 2011. This is clear evidence that the NSA had a hand in the development of UEFI itself as a cyber weapon for the NSA. I first learned about UEFI from a speech given by Bill Gates on May 23, 2006. Here is a quote from Bill the day he announced UEFI to the world:
UEFI version 1.0 in 2006 was not that different from BIOS. In particular, it did not include secure boot. Neither did UEFI version 2.1 which was released on January 7, 2007. So what the heck was Bill Gates talking about in his 2006 speech when he referred to a “new capability”? Little did we know then that by “us” Bill was referring to his Prism Partners at the NSA and that by “new capability” Bill meant that the NSA would soon be able to hack into any computer on the planet by hacking into the new back doors they placed in the UEFI BIOS.
In my previous article, I detailed the entire history of how UEFI was started by the NSA in 2007 and evolved over several years into the cyber weapon it is today. I will not repeat all of that here. But if you still think that UEFI is some sort of friendly product created by a non-profit group then you need to read the following article. https://learnlinuxandlibreoffice.org/news/the-fight-for-a-secure-linux-bios
You can also view a video presentation of this article at the following link: https://www.youtube.com/watch?v=mEPcRFvvekY
The article and presentation provide dozens of links and a complete history of this hacking tool starting in 2007 and ending with the latest version in April 2019. This NSA UEFI hacking tool while well known in the hacker world, surprisingly has no official sounding name – despite being the most dangerous hacking tool in history. This is why I now refer to this UEFI hacking tool as Xbot – the bot with no name. What nearly all of these NSA-based cyber weapons have in common is that they were specifically designed for Windows computers running the UEFI BIOS program. The method they use to achieve real persistence is what the NSA originally called Berserkrk and later called Sierra Mist and I now call Xbot.
Xbot gives Trickbot and Ryuk cyber weapons what the NSA called “persistence.” Persistence means that NSA-based malware, including Trickbot and Ryuk can survive replacing the operating system and even replacing the hard drive. These extremely complex hacking tools can hide in several places including in the computer firmware, the computer RAM chips and even in the computer central processing units.
This included “persistent” control over not only the operating systems, databases, backups and other programs but also the hard drives, firmware and even the Central Processing Units. It is because of this persistent control that Ryuk Ransomware includes a message warning victims to not turn off their computers – because the malware buried in the UEFI BIOS of the firmware will then corrupt the data in the computer making it impossible to recover. You will not find any online links between Xbot, UEFI and Ryuk. But hackers who are capable of combining Trickbot with Ryuk are clearly capable of combining Xbot with Ryuk.
Here is an April 2017 Video on UEFI Ransomware
https://www.youtube.com/watch?v=xYrcaa1fSXA&t=130s
Here is what your screen looks like at the end of this 5 minute video:
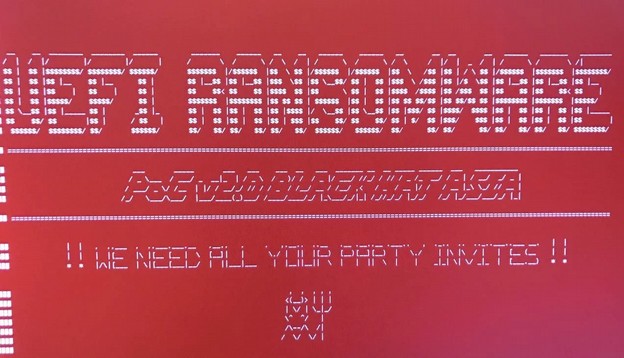
At the Black Hat Asia 2017 security conference, researchers from Cylance disclosed two more vulnerabilities which allow an attacker to write malicious content to the UEFI firmware. They noted the same flaws can be used to plant rootkits that allow attackers to persist malware for years.
In this April 2018 video a 20 year old hacker explains how to hack UEFI in 13 minutes. “You do not need to know much “Because UEFI is badly written software. I call this the Lord of the Rings attack Others call it the SMM attack. SMM is controlling everything “ https://www.youtube.com/watch?v=lzZvL1wZ-WM

If a 20 year old kids knows how to implant Xbot, you can bet that professional hackers also know how to do the same.