IX. How to Recover & Protect Yourself from Future Attacks
Now that we have a better understanding of how Emotet, Trickbot, Xbot, Ryuk and Mega Cortex work, we can consider how to really recover from a Ryuk Ransomware attack and truly protect your computer network from future attacks. This sadly it an area where Ryuk victims have been given extremely bad advice. First, these victims are attacked by Ryuk and often wind up paying a huge ransom for temporary relief. Then these same victims fall pry to so-called “security experts” who give them very expensive advice that does not even remotely solve the long term problem of avoiding not only Ryuk but also avoiding future attacks by Emotet, Trickbot and Xbot. So before we consider how to really recover from a Ryuk attack, let’s look at some typical advice and why none of what Ryuk victims are currently being told solves the long term problems.
Stockholm Syndrome… Blaming the Victims
What is most distressing about the advice given to victims of ransomware attacks is that nearly all of this advice blames the victim for the attack. If only they had better backups. If only they had done more staff training. If only they had installed the latest Windows update or the latest anti-virus software. Stockholm Syndrome has been defined as “the psychological tendency to blame the victims of a crime for being partially or completely responsible for the crime that was committed against them.”
Let’s take a closer look at advice being given to victims to see why it will not actually solve the underlying causes of the ransomware problem:
#1 Why Backups are not an effective solution to the Ryuk Problem
Many so-called security experts falsely claim that all you need to do is keep offline backups of your network and use these backups to replace your encrypted data should your network become a victim. What these experts fail to understand is that Trickbot has tools to implant itself in the backups. Trickbot often spends months infecting these backups. So unless the backup is more than a year old, the backups could also be contaminated. The backup may appear to work for a while. But if it also is contaminated, another ransom demand is likely to be issued in the future.
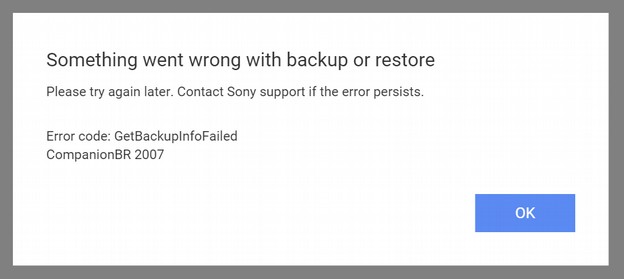
To be clear, I am not saying to skip backups. You should have both externally stored backups and cloud based backups with syncing tools for both. These are useful for solving other problems. However, backups by themselves will not solve the Ryuk Ransomware problem.
#2 Staff Training to not click on links is not an effective solution
Another naive bit of advice is to better train staff how to recognize malicious email attachments – or even prevent staff from downloading attachments or clicking on links altogether. While staff training might reduce the chances of downloading Emotet and Trickbot in the first place, once Trickbot is downloaded, it goes about stealing passwords and credentials without any further need to be downloaded again. Moreover, staff should be expected to download files and click on links as an effective part of doing their research. The last thing staff should be told is to be afraid to click on a link. What if the link actually is about an important invoice or UPS shipment?
It it true that you can avoid security problems by never letting your staff go online. But this ignores the ultimate source of the problem. The problem is not your staff downloading attachments and clicking on links. The problem is that the Windows operating system is so insecure that hackers can use normal staff activities to infect the Windows operating system. Blaming your staff is like blaming the victim for being attacked.
The problem in its most simple terms is that Bill Gates made a mistake in 1998 when he placed the Internet Explorer Web Browser inside the core of the Windows operating system. The Windows operating system has been insecure ever since. There is no solution to this problem other than to replace the Windows operating system with a more secure operating system that does not have the web browser inside the core.
Even if no one on your network downloads any more infected Microsoft Office documents and even if your backup was not corrupted, as long as you are using the Windows operating system and UEFI BIOS, the malware can hide in several other parts of your computer network. Again, your network may appear to have recovered only to be subject to additional hacking attacks in the future.
Instead, if you switch to a more secure operating system, such as Linux, your staff can click on whatever links they want and download whatever attachments they want. Even if they download a malicious Word document, it will not be able to infect the Linux operating system or travel from computer to computer across the network because Linux has a much more secure file structure and permissions structure than Windows.
#3 Forcing Staff to use Longer or Two Factor Passwords is not a solution
While longer passwords and two factor authentication may help protect against brute force attacks, neither Ryuk or Mega Cortex are brute force attacks. Both use much more subtle methods to get inside your computer network. Once inside, it does not matter how long the passwords are or where they are stored. This is because Trickbot has tools to gather up all administrator passwords. So long passwords and two factor passwords are at best a distraction and at worst lead to a false sense of security.
#4 Antivirus Programs are not an effective long term solution
Third, many so-called experts sell Ryuk victims one or more commercial anti-virus solutions. However, none of these anti-virus programs can completely protect Windows computers because Windows computers suffer from several fundamental security flaws. Anti-virus program providers do not want you to be cured from this disease because they make money by providing monthly fixes for what is in fact an insecure Windows operating system. By contrast, ant-virus programs are not needed on Linux computers because there is no open back door into the core of the Linux operating system to begin with.
#5 Upgrading from Windows 7 to Windows 10 is not a solution
Neither is upgrading from Windows 7 to Windows 10 a solution to the Ryuk problem. In fact, Windows 10 is less secure than was Windows 7. Even its normal update process, Windows 10 has crashed millions of computers – without any malware attacks. This is because Windows 10 has three major problems that Windows 7 did not have.
The first problem is that Microsoft executives (against the advice of their own programmers) introduced a second control panel with Windows 8 and continued this second control panel with Windows 10. As only some of the functions were migrated to the second control panel, the first control panel is still on Windows 10. This creates huge stability problems which is why Windows 10 computers are so prone to crashing. It is like having two pilots trying to control and fly the same plane at the same time. The right hand never knows what the left hand is doing and the plane occasionally crashes into the ground.
The second problem is because each control panel needs a way to communicate with the Mother Ship (Microsoft), Windows 8 also introduced a second web browser into the core of their operating system. This second web browser is in fact a second back door into the Windows 8 and Windows 10 operating system.
Third and most important, Windows 8 and Windows 10 do not work with what is now called Legacy BIOS. Both only work with UEFI BIOS. As I explained earlier and wrote about extensively in my previous article, UEFI BIOS was developed by the NSA and is itself basically a cyber weapon. UEFI BIOS is what gives the NSA (and hackers who mimic the NSA) persistent access to your computer network even if you replace the Windows operating system and the hard drives.
#6 Updating Windows is not an effective long term solution
Finally, many so-called security experts claim that all you need to do is install the latest Windows operating system patches. These patches have a long history of not working and causing computer networks to crash even if they are not infected with Ryuk Ransomware. Microsoft issues updates on the second Tuesday of every month. This has become known as Patch Tuesday. The not so funny joke is that Patch Tuesday is followed by Crash Wednesday.
As examples of how futile Windows Updates are, just look at the past two Windows monthly updates. On August 13 2019, Microsoft released patches for 93 security flaws. The most dangerous of these flaws were four remote code execution (RCE) flaws that take advantage of holes in Windows Remote Desktop Service (RDS). The numbers for these flaws are CVE-2019-1181, CVE-2019-1182, CVE-2019-1222, and CVE-2019-1226. For those keeping score, this is the fourth time in 2019 Microsoft has had to fix critical security issues with its Remote Desktop service.
But the notice included a total of 29 remote execution flaws affecting nearly every type of Windows program from MS Word to MS Outlook. Hackers can exploit any of these 29 Remote Code Execution flaws to take over a computer and then spread malware to other computers on the same network without any user interaction.
The Security Update Guide for August 2019 explaining all of these flaws was over 100 pages long. This is based on the following Microsoft link which lists 20 flaws per page and has a total of 2355 items divided over 118 pages. But the Excel spreadsheet for all of the flaws actually listed 2,977 flaws being patched. The file size for just the August 2019 Update was 1038 Megabytes (over 1 Gigabyte).
https://www.catalog.update.microsoft.com/Search.aspx?q=KB4512497
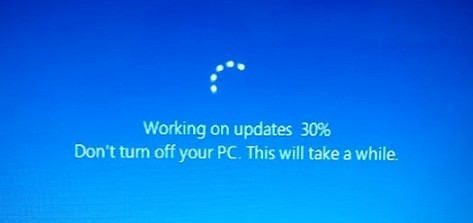
Nor was this unusual for Microsoft to have dozens of security flaws revealed in a single month. The July 2019 Windows Update attempted to fix almost 80 security holes in the Windows operating systems and related software. Among them were patches for two zero-day flaws that are actively being exploited in the wild. Every month, dozens of patches are issued for dozens of security holes. None of the patches actually fix the holes which is why a new round of additional patches are needed each month.
All the patches really do is create their own problems which every month cause millions of Windows computers to crash. Many computer network operators have attempted to avoid these problems by not updating to Windows 10. However, Microsoft has announced that in January 2020, they are ending support for both Windows 7 and Legacy BIOS. This is intended to force all users to adopt Windows 10 and UEFI BIOS regardless of how insecure those options are.
But the problem with forcing the entire world to use the same top down monopoly based operating system and BIOS system is that, while this makes it easier for Microsoft and the NSA to control our computers, it also makes it easier for hackers to hack our computers.
The Real Solution to Prevent Future Ryuk Attacks is to Switch to Linux OS and Linux BIOS
The only real solution to Ryuk, Trickbot, WannaCry, Not Petya and all other NSA based Windows based hacking tools is to move away from the poorly designed Windows operating system to the vastly more secure Linux Operating system. Linux does not keep the web browser inside of the core of the operating system. Thus, there are no easy back doors into the Linux operating system. This is why none of the current ransomware tools work on Linux computer networks. This is why large corporations like Google, Facebook and Amazon long ago moved their millions of servers to Linux. Google, Facebook and Amazon have also invested millions of dollars in non-UEFI based BIOS programs. These include Coreboot and Linux BIOS.
Sadly, not all current computers are compatible with Coreboot or Linux BIOS. Thankfully, all Google Chromebooks use Coreboot. I am writing this article on an Acer C910 laptop that came with Coreboot. I reflashed the Coreboot BIOS to run a full Linux operating system rather than the striped down and limited Chrome operating system that comes with Chromebook laptops. Purism is another maker of fulling functioning Linux computers that come with Coreboot. Several other computer manufacturers have announced plans to switch to Coreboot. Hopefully, they can make the switch before January 2020.
In 2014, even Microsoft began the switch from the Windows operating system to the Linux operating system.

Since 2014, Microsoft has migrated nearly one million servers on their server farm in Quincy Washington from Windows to Linux. Microsoft has also fired tens of thousands of Windows programmers and replaced them with tens of thousands of Linux programmers.
Most recently, IBM has paid $34 billion to purchase a Linux computer service company called Redhat. Nearly all mobile phones also run on Redhat. So the real question is given that Windows vulnerabilities have cost them billions of dollars in ransomware attacks, why have many businesses and colleges been so slow to make the transition from Windows to Linux?
The most common answer is that businesses, schools and colleges are “addicted” to using Windows programs like Microsoft Office (note that the word addicted is a word Bill Gates used to explain why people get hooked on using Windows programs).
Addressing Concerns about Switching from Windows to Linux
First there are typically good free secure open source alternatives to Windows programs. In particular, for years, we have been able to open, edit and save all Microsoft document formats using a free, open source and secure Word Processing program called Libre Office. There are entire websites devoted to doing nothing but providing lists of free open source Linux programs as alternatives to insecure Windows programs.
Second Windows programs can be run inside of the Linux operating system using Wine. Even if you come across a Windows program that does not have an equal or better Linux alternative, you can simply run normal Windows programs inside of Linux using a Linux program called WINE. Again, this function has been around for years.
Third, Windows programs can also be used inside of Windows using a Virtual machine. If you do not want to use Linux alternative programs and do not want to run Windows programs inside of WINE, you can also run Windows programs on the Windows operating system but place the Windows operating system inside of a virtual machine that is running inside of Linux. Virtual machines are much more difficult to hack and much more secure than using Windows as the base operating system.
So the real problem is simply that people are creatures of habit. They are afraid to try new things. But at some point, users are going to say enough it enough. Ryuk and Mega Cortex Ransomware may just be the tipping point into finally convincing corporations, schools and colleges that the time is long past due to move away from Windows to the much more secure Linux operating system.
Four Ways to Try Linux
Some folks think that it is very hard to learn Linux. While some versions of Linux are intended for computer programmers and therefore can be hard to learn, there is a very simple version of Linux called Linux Mint which looks and acts almost exactly like Windows 7. There are several ways to try Linux Mint before making the jump from Windows to Linux.
First, you can install a free program onto any Windows computer called Virtual Box and then load Linux Mint into Virtual Box. I have written instructions for how to do this are on this page: https://learnlinuxandlibreoffice.org/2-linux-to-the-rescue/2-2-take-linux-mint-for-a-test-drive
Second, you can create a create a Linux Mint Live Stick and install it on any old computer that no longer works with Windows 10. Windows 10 requires at least 4 GB of RAM while Linux Mint only requires 2 GB of RAM. If you have an old computer, instead of throwing it away, just replace Windows 7 or whatever else was on it with Linux Mint. It takes less than one hour and your old computer will run better and faster than the day it was new. I have written instructions on how to create a Linux Mint Live stick and install it on any computer on this page: https://learnlinuxandlibreoffice.org/3-create-your-own-linux-computer/3-4-install-linux-mint-on-an-acer-c910-chromebook
Third, if you do not have an old computer to convert and do not want to install Virtual Box on your current computer, you can also try Linux Mint without installing it by setting any computer to boot from a USB stick and then inserting a Linux Mint Live stick into a USB port and turning on the computer. You can practice using Linux without it affecting the hard drive in any way. The only problem with this method is that none of the documents you create will be saved when you turn off the computer.
Fourth, you can create a Linux Mint Persistent Stick, also called a computer on a stick. This is very similar to using a Live Stick to install Linux Mint to the main computer hard drive. Only instead of installing Linux Mint to the computer hard drive, you stick another USB stick in a second USB port and use the Mint Live Stick to install Linux onto the Linux Persistent Stick.
This method of creating a computer on a stick is ideal for teachers and students because it allows them to use a school’s computer lab without altering in any way any of the computers in the lab. Students can save their work and bring their Linux Mint Persistent sticks home and continue to practice using Linux on any computer they may have at their home. Students can even keep their Linux Mint live sticks to continue practicing with even after the course is over. All that is required is about $10 for a USB 3 drive that is 8 to 16 GB to create the Mint Live Stick and about $20 each for a USB 3 drive that is 64 GB to 128 GB to create the Mint Persistent stick. I have written instructions for how to do this at the following page: https://learnlinuxandlibreoffice.org/2-linux-to-the-rescue/2-3-create-a-usb-stick-with-persistent-storage
Switching your computer(s) from Windows to Linux is the best way to protect your computer network from Ryuk Ransomware. But given the harm this new malware is inflicting on computers around the world, what we really need is to train the next generation how to put an end to Ryuk and all other ransomware. That is the subject of the next section.